If you have Atlassian Confluence deployed, you probably have received notification of the latest security advisory on a critical vulnerability discovered by Volexity that allows for unauthenticated remote code execution on servers running Atlassian’s Confluence Server and Data Center applications. On June 2, 2022, Atlassian issued the CVE-2022-26134 advisory.
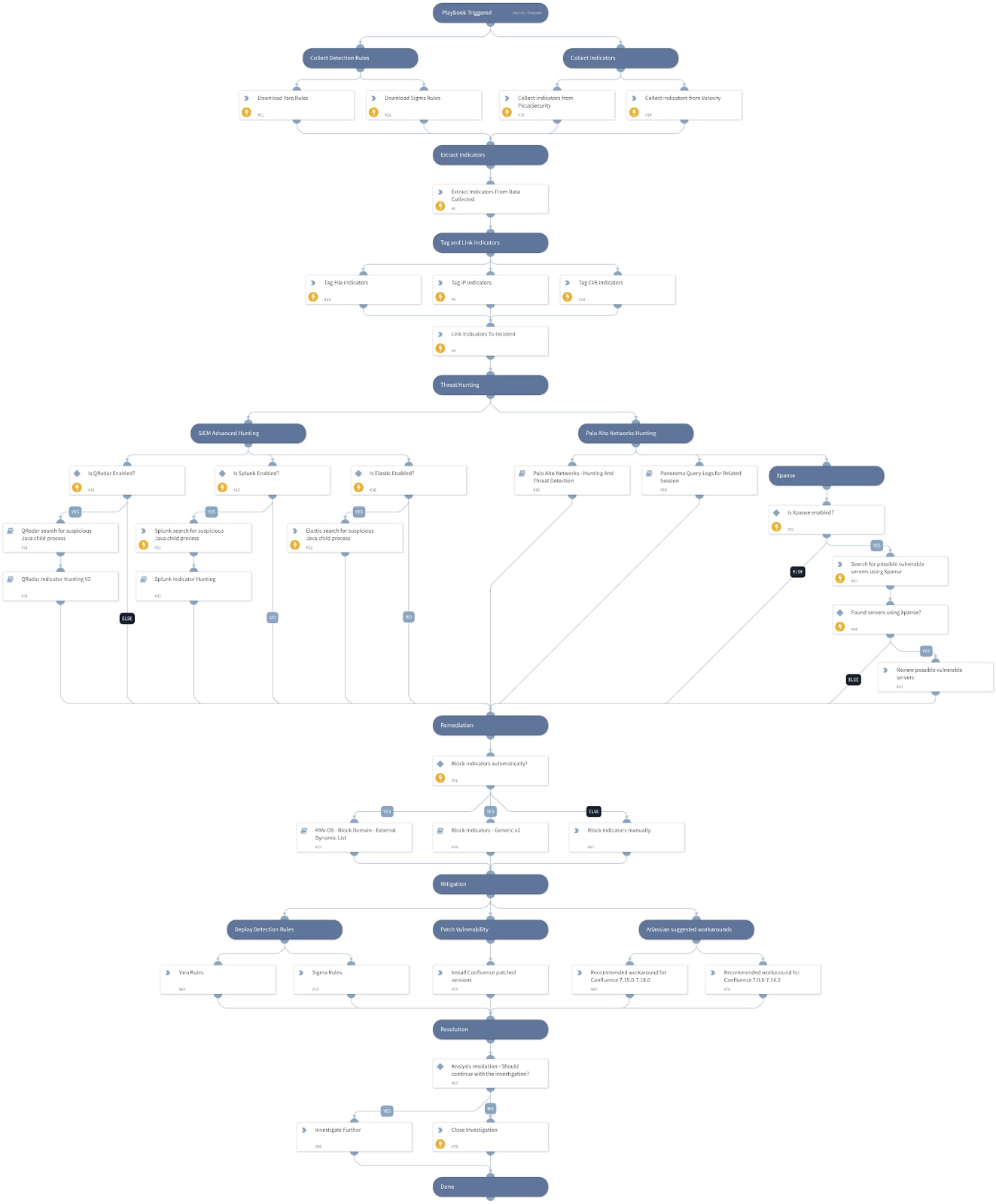
Now your team is hard at work tracking and patching this vulnerability, and we have just the automation playbook to help your team orchestrate response across your Palo Alto Networks environment and SIEMs. Reduce manual effort and speed up the patching process by using our Cortex™ XSOAR playbook to:
- Automate incident data enrichment
- Collect detection rules that indicate potential successful exploitation of the CVE-2022-26134
- Extract and tag the indicators (file, IP, CVE)
- Link indicators to incidents in your environment
- Automate threat hunting
- Search for exploitation patterns and associated indicators of compromise (IoCs) across your SIEM
- Query your Palo Alto Networks firewalls and Panorama logs for related sessions
- Search for possible vulnerable servers using Cortex® Xpanse™
- Take remediation actions
- Block indicators automatically at your PAN-OS enforcement points
- Deploy Yara and Sigma detection rules
- Install Confluence patched versions
- Surface Atlassian recommended workarounds to your team for quick follow-up
This playbook is part of the Rapid Breach Response Pack which includes various playbooks for trending vulnerabilities and threats. If you are running XSOAR 6.8 you can subscribe to pack updates and get notifications for quick response.
Rapid Response Playbook for Atlassian Confluence Zero-Day Vulnerability
For more information about the vulnerability, check out our Unit42 and Atlassian Confluence advisories. You can get more details on our playbook here.
To learn more about how you can automate security operations with Cortex XSOAR, check out our virtual self-guided XSOAR Product Tour
We also host virtual and in-person events, so check here for upcoming ones.