Microsoft recently warned Windows users about two vulnerabilities, CVE-2021-1675 & CVE 2021-34527, affecting the Windows Print Spooler Service. Proof-of-concept exploit code was posted on Github before the vulnerabilities were fully patched.
The incident, dubbed by the security community as "PrintNightmare," allows threat actors to exploit remote code execution (RCE) vulnerabilities and run arbitrary code with system privileges.
Palo Alto Networks recommends that Windows users update their operating systems as soon as possible to patch the vulnerabilities. Organizations can also block PrintNightmare exploits with Cortex XDR; read on to learn how.
Cortex XDR Response
Cortex XDR agent 7.4.1 with content version 189-64538 and above is capable of preventing all currently known implementations of the exploits on vulnerable hosts, including patched hosts with the “Point and Print” feature enabled.
What the user should expect when running Cortex XDR agent 7.4.1:
Alert from a patched Microsoft Windows host:
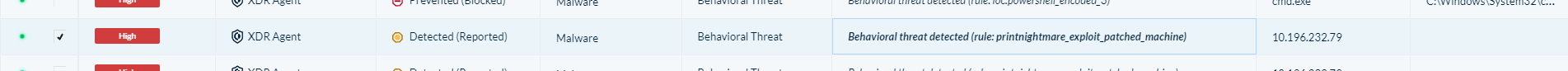
Figure 1: A PrintNightmare alert in the Cortex XDR Alerts table. Cortex XDR detected an exploit attempt that was blocked by the Windows patch.
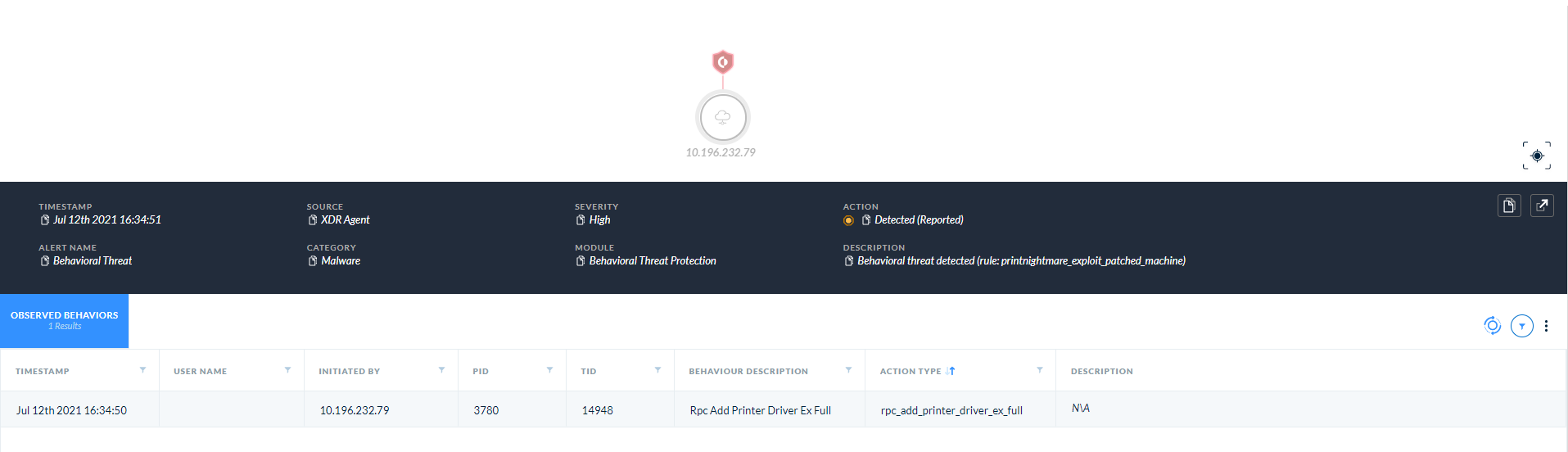
Figure 2: An alert card showing a detected exploit attempt.
Alert from an unpatched Microsoft Windows host:
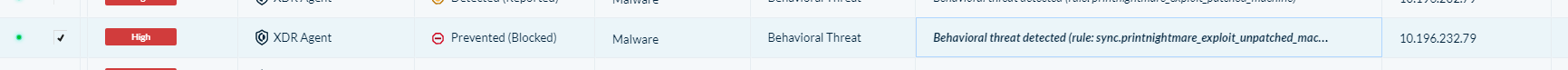
Figure 3: Cortex XDR blocked the malicious RPC operation.
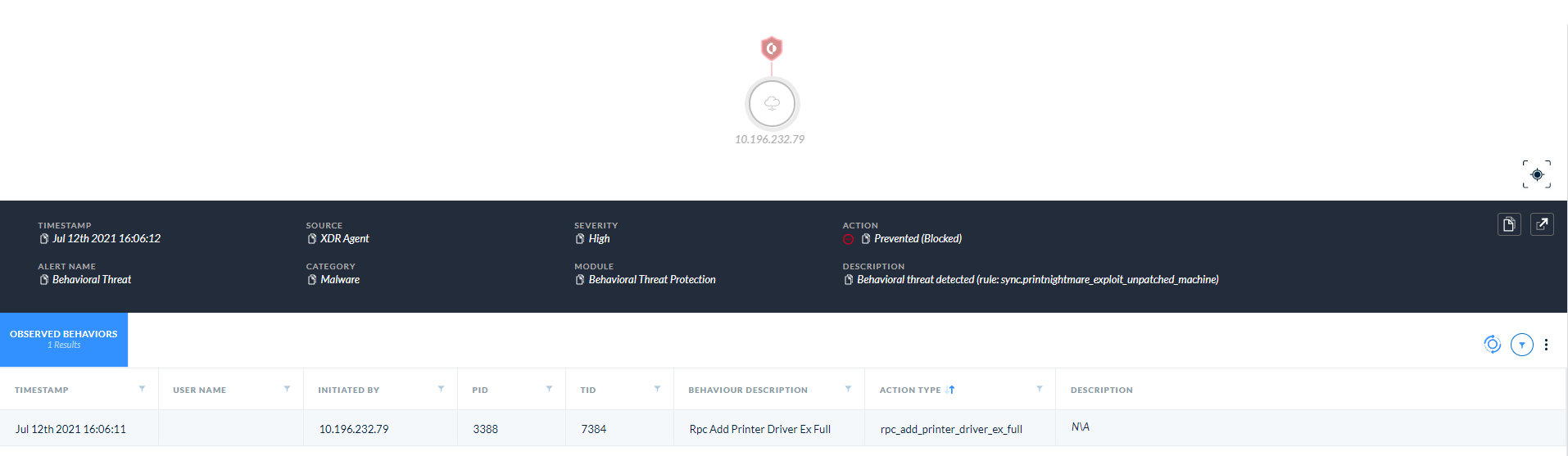
Figure 4: An alert card showing a blocked exploit attempt.
Distinguishing between local and remote exploits
Note that the difference between the two cases will be seen in the “initiated by” field. For a local case, you will see a process name on the machine; for a remote case, you will see an IP address for a machine inside your network.
Alert Severity
When alerting on an exploitation attempt targeting a patched machine, Cortex XDR usually labels these alerts as “low” severity. In this case, Cortex XDR will rate the patched machine alerts as high severity since an attacker is already inside your network (for the RCE case) or even on your machine (for the local privilege escalation case). We highly recommend investigating those alerts and not ignoring them even if the machine is already patched.
References & Additional Information
- Hunting PrintNightmare with XDR - /blog/security-operations/hunting-printnightmare/
- Remediation of printNightmare with XSOAR - /blog/security-operations/remediating-printnightmare-cve-2021-1675-using-cortex-xsoar/
- Threat Brief: Windows Print Spooler RCE Vulnerability (CVE-2021-34527 AKA PrintNightmare) https://unit42.paloaltonetworks.com/cve-2021-34527-printnightmare/