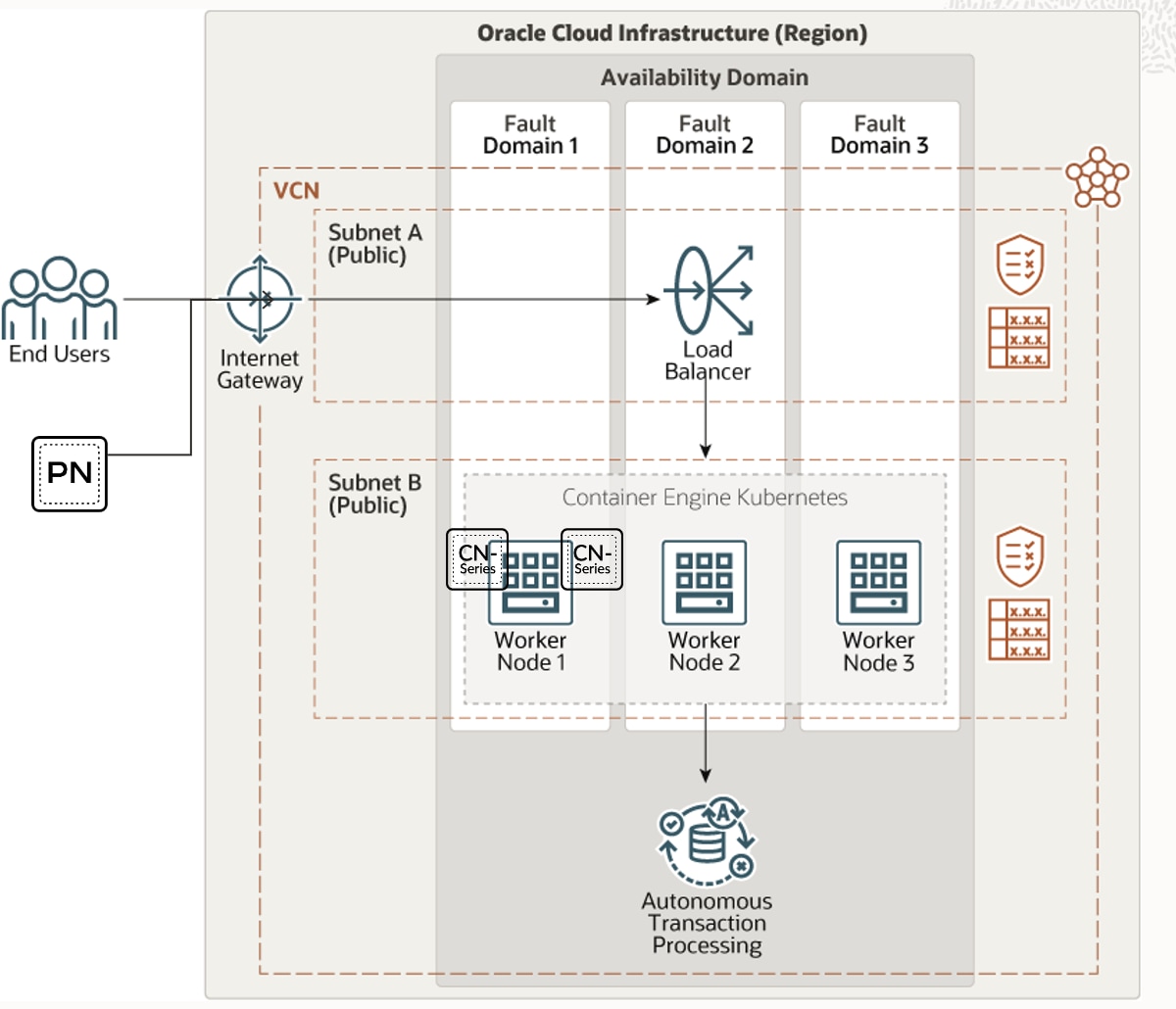
We’re pleased to announce the availability of CN-Series Container Firewalls on Oracle Cloud Infrastructure. With this release, customers can use CN-Series container firewalls to protect applications running on Oracle Kubernetes Engine (OKE) clusters.
OKE has been designed to reduce the time and cost that go into building modern cloud-native applications. With the Oracle-managed container orchestration service, DevOps engineers can use unmodified, open-source Kubernetes for application workload portability. With automatic updates and patching, the service opens up the potential for more productivity. Not only that, they can also use Helm Charts to streamline the deployment of container workloads.
Network Security Needs to Extend to Containers
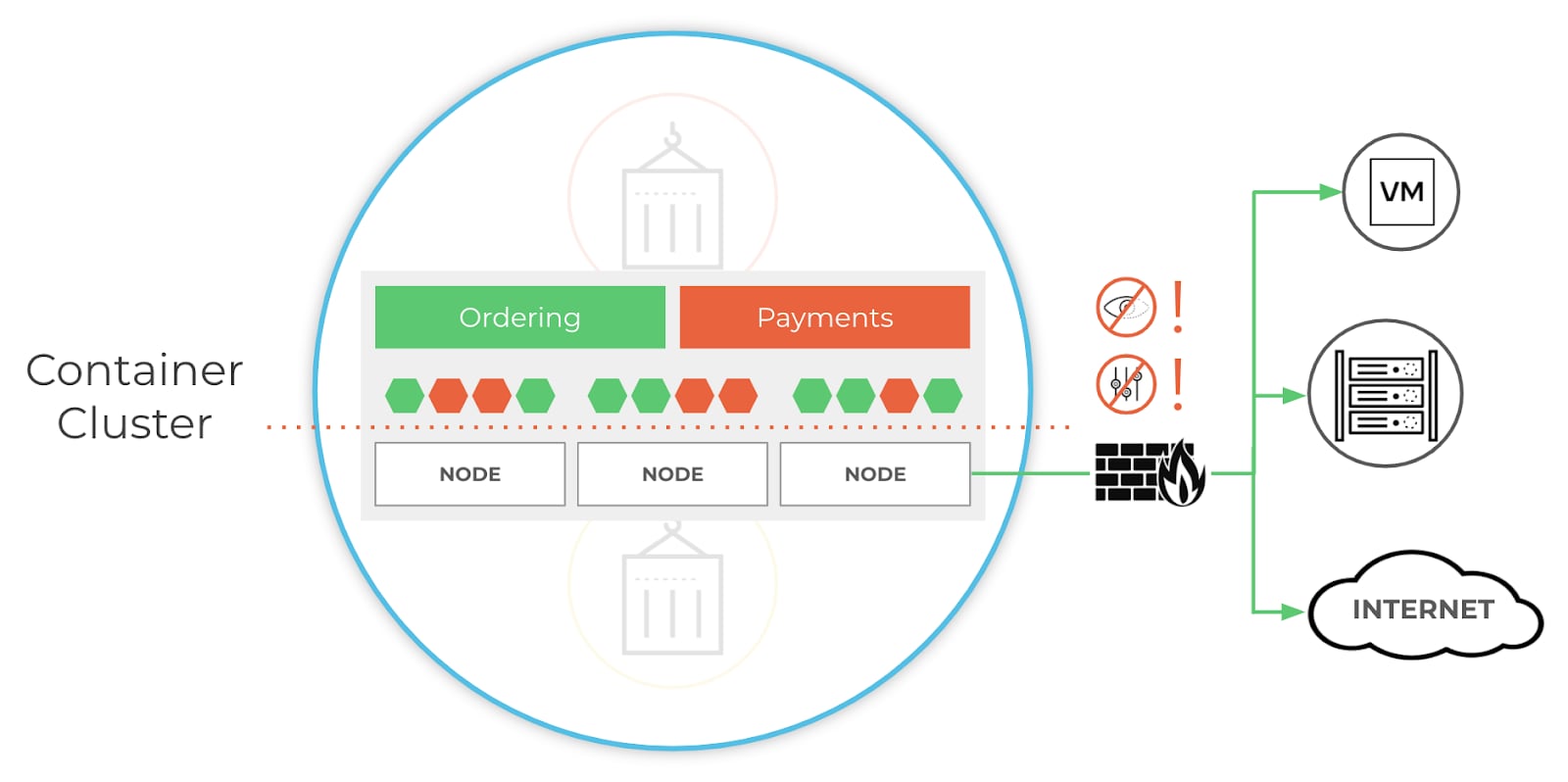
For the uninitiated, containers may seem like a secure option for running applications. But in reality, network-based threats still apply to this revolutionary approach to operating system virtualization. Unfortunately, network security teams often lack container expertise and may not have the necessary tools to secure containerized apps. This can lead to a fragmented security posture, which can leave modern apps vulnerable to attacks.
Without easy access to the tools that secure containerized applications, network security teams have limited visibility and control over container traffic. This often results in slowing down important development efforts and can cause serious frustration between development and network security teams.
CN-Series Takes on Container Vulnerabilities
Thankfully, there is a solution to this problem. The Palo Alto Networks CN-Series container firewall is the first next-generation firewall purpose-built to secure Kubernetes orchestration environments from network-based attacks. The CN-Series firewall enables network security teams to gain layer-7 visibility into Kubernetes environments, provide inline threat protection for containerized applications deployed anywhere, and dynamically scale security without compromising DevOps agility.
And that’s a big deal for customers with containerized applications running on OKE. Organizations can now:
- Scale CPU and memory usage for applications
- Specify optimal deployment type (Daemon set mode or Kubernetes Service Mode)
- Easily configure the deployment of CN-series Container Firewall to protect containerized applications using YAML files or Helm Charts
CN-Series ensures frictionless continuous integration/continuous development (CI/CD) pipeline deployment while delivering unparalleled runtime network protection through unified management across all multiple firewalls.
With CN-series available on Oracle Kubernetes Engine (OKE), customers can now deploy CN-series to protect their containerized applications running on OKE.
Understand the Importance of Helm Charts
Kubernetes has made container-orchestration incredibly easy, but dealing with Kubernetes objects can be complex. That’s where Helm Chart comes in: This popular package manager speeds the installation, updating, and upgrading of complex Kubernetes applications.
That’s also a big deal, because Helm Charts allows you to:
- Deploy Kubernetes packages using the command line.
- Streamline deployment of container workloads through CI/CD pipeline as well enable teams to automate pre-and post-deployment actions.
- Customize application configurations so that the Helm Charts can be reused across multiple environments.
By deploying CN-series in OKE using Helm charts, you can simplify the deployment, and reduce duplication and complexity in deploying containerized workloads. What’s more, you can diminish the time required to publish the applications quickly, which can substantially boost productivity.
Get Started with CN-Series and OKE
You can get started with CN-Series and OKE today by contacting our sales team or just ask us for a personalized demo. For more information about securing Kubernetes orchestration across environments check out the CN-Series YouTube Channel.
_
Arun Poonia is a Principal Solutions Architect at Oracle whose work is currently focused on Oracle Cloud Infrastructure Network & Security Partners. His experience over the last 10 years has been around architecting, designing, integrating, automation of different key partners and associated customers solutions in a hybrid cloud environment.