- What Is the Difference Between IoT and OT Security?
-
What Is the Purdue Model for ICS Security? | A Guide to PERA
- How does the Purdue Model for ICS Security work?
- What are the Purdue Model layers?
- What are industrial control systems?
- What are the main ICS architecture security challenges?
- What kinds of cyberthreats commonly impact ICS?
- What is the history of the Purdue Model?
- Examining the Purdue Model’s role in modern ICS security
- Purdue Model for ICS Security FAQs
- What is OT security?
-
What Is IT/OT Convergence?
- What Is OT?
- What Is the Difference Between IT and OT?
- How and Why IT and OT Are Converging
- Types of IT/OT Convergence
- The Role of IoT and IIoT in IT/OT Convergence
- IT/OT Security Convergence
- Impacts of IT/OT Convergence on ICS Security
- IT/OT Convergence Benefits
- IT/OT Convergence Challenges
- IT/OT Convergence Use Cases and Examples
- IT/OT Convergence Best Practices
- IT/OT Convergence FAQs
- What Is Internet of Medical Things (IoMT) Security?
-
What Is ICS Security? | Industrial Control Systems Security
- What is an ICS?
- Why is ICS security important?
- How does ICS security work?
- What is the role of IT/OT convergence in ICS security?
- What kinds of cyberthreats commonly impact ICSs?
- What are the main ICS security challenges?
- What are the primary ICS protocols?
- How to achieve ICS security step-by-step
- 10 ICS security best practices
- What are the primary ICS security frameworks, standards, and regulations?
- What is ICS supply chain security?
- 2025 ICS security market and trends
- What are the different types of industrial control systems?
- What are the components of an industrial control system?
- What are the differences between OT, ICS, SCADA, and DCS?
- How does ICS security compare with OT and SCADA security?
- What is the history of industrial control systems?
- ICS security FAQs
-
What Is Cyber-Physical Systems Security (CPSSEC)? | Overview
- What are examples of cyber-physical systems?
- What is the difference between a cyber-physical system and an Internet of Things (IoT) device?
- Why is cyber-physical system security important?
- What are the common cyber-physical system security challenges?
- What to look for in a CPS protection platform
- Cyber-physical systems security FAQs
- What Is Critical Infrastructure? Why Does Critical Infrastructure Security Matter?
- What is 5G security?
- IT vs. OT Security | What Are the Differences?
- What Are the Differences Between OT, ICS, & SCADA Security?
- What Is the Difference Between IT and OT? | IT vs. OT
-
How to Secure IoT Devices in the Enterprise
-
The Impact of IT-OT Convergence on ICS Security
-
Building Secure Smart Cities in the Age of 5G and IoT
What is IoT Security?
While relatively new as a cybersecurity discipline, the Internet of Things (IoT) as a business enabler has matured into a clearly defined set of use cases solving pressing business problems that deliver operational and cost benefits across many industries, such as healthcare, retail, financial services, utilities, transportation and manufacturing.
The rapid growth of capabilities and adoption of IoT technology has fueled a transformation in enterprise operations with IoT devices making up 30% of total devices on enterprise networks today. Rich data collected from these devices provides valuable insights that inform real-time decisions and deliver accurate predictive modeling. In addition, IoT is a key enabler of digital transformation in the enterprise, with the potential to drive up workforce productivity, business efficiency and profitability as well as the overall employee experience.
Despite the many advantages and innovations IoT technology enables, the interconnectedness of smart devices presents a substantial challenge to enterprises in terms of grave security risks arising from unmonitored and unsecured devices connected to the network.
Related Video
IoT Security with Dr. May Wang (Part 1)
What Is an IoT device?
An IoT device is essentially any network-connected physical asset that isn't a computer. While enterprise IT teams protect standard IT devices with traditional network security technology and protocols, the security risks associated with IoT devices are less well-known, and securing IoT is an unaddressed challenge in many organizations. Standard cybersecurity systems are incapable of recognizing and identifying either the specific types of IoT devices or the unique risk profiles and expected behaviors associated with them.
In addition, IoT devices can be deployed by any business center, thereby bypassing typical network security controls and processes. All of these network-connected IoT devices – printers, cameras, sensors, lighting, HVAC, appliances, infusion pumps, handheld scanners (the list goes on and on) – are using different hardware, chipsets, operating systems and firmware that introduce vulnerabilities and risk.
What Are the Challenges of IoT Security?
IoT security can be understood as a cybersecurity strategy and protection mechanism that safeguards against the possibility of cyberattacks which specifically target physical IoT devices that are connected to the network. Without robust security, any connected IoT device is vulnerable to breach, compromise and control by a bad actor to ultimately infiltrate, steal user data and bring down systems.
The overarching challenge for security in IoT is that as large volumes of diverse IoT devices continue to connect to the network, a dramatic expansion of the attack surface is happening in parallel. Ultimately the entire network security posture is diminished to the level of integrity and protection offered to the least secure device.
Security teams are now faced with new and escalating challenges that are unique to IoT security, including:
Inventory – not having clear visibility and context for what IoT devices are in the network and how to securely manage new devices.
Threats – lack of well-embedded security into IoT device operating systems that are hard or impossible to patch.
Data volume – overseeing vast amounts of data generated from both managed and unmanaged IoT devices.
Ownership – new risks associated with the management of IoT devices by disparate teams within the organization.
Diversity – the sheer diversity of IoT devices in terms of their limitless forms and functions.
Operations – the unification crisis wherein IoT devices are critical to core operations yet difficult for IT to integrate into the core security posture.
In addition to these challenges, 98% of all IoT device traffic is unencrypted, putting personal and confidential data at severe risk.
Every IoT device on the network represents an endpoint which provides a potential point of entry for a bad actor to expose the network to outside risks. This includes the IoT devices you know about as well as the IoT devices you don't know about. For example, if infected with malware, IoT devices can be used as botnets to launch distributed denial-of-service (DDoS) attacks on the network the bad actor wants to bring down. However, unlike IT devices, a growing number of IoT devices are virtually invisible in enterprise networks, making it impossible to protect them all in the same way.
Which IoT Devices Have the Highest Share of Security Issues?
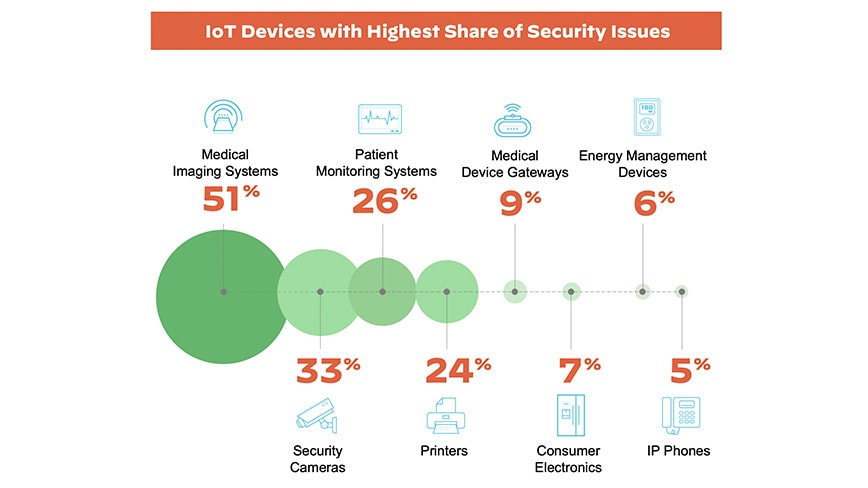
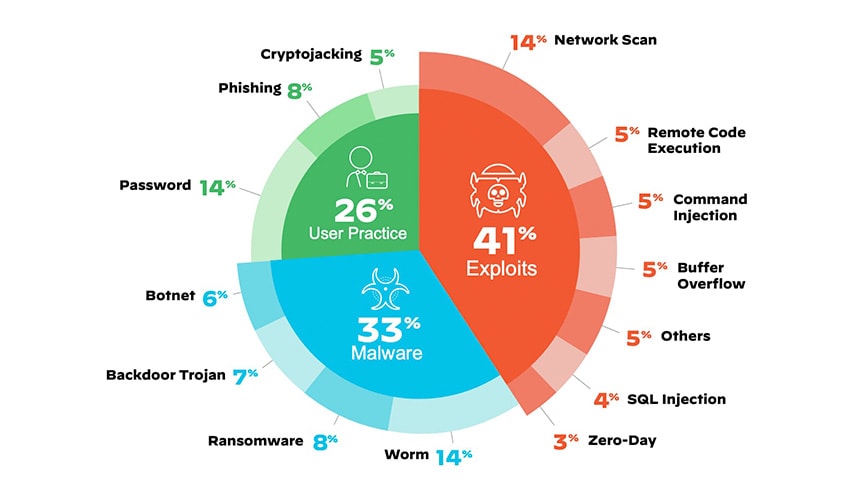
Some of the most frequent attacks on IoT devices are exploits executed using techniques such as network scanning, remote code execution, command injection and others. Forty-one percent of attacks exploit device vulnerabilities, as IT-borne attacks scan through network-connected devices in an attempt to exploit known weaknesses. After compromising the first device, lateral movement is opened up to access other vulnerable devices and compromise them one by one.
What Are the Top IoT Security Threats?
Besides using some of these time-tested attack tactics thought obsolete by modern IT-based malware prevention, peer-to-peer command-and-control (C2) communication and self-propagating IoT malware worms are two new attack tactics emerging on the IoT security horizon. IoT worms are, in fact, becoming more common than IoT botnets. Both tactics target decades-old legacy OT protocols to disrupt critical business operations in the enterprise.
What Are the Best Practices for IoT Security?
Strategically minded CISOs and security leaders are moving beyond legacy network security solutions and taking a complete IoT lifecycle approach, creating an IoT security posture that reliably enables IoT innovation and protects the network from existing and unknown threats. The lifecycle approach encompasses five critical stages of IoT security.
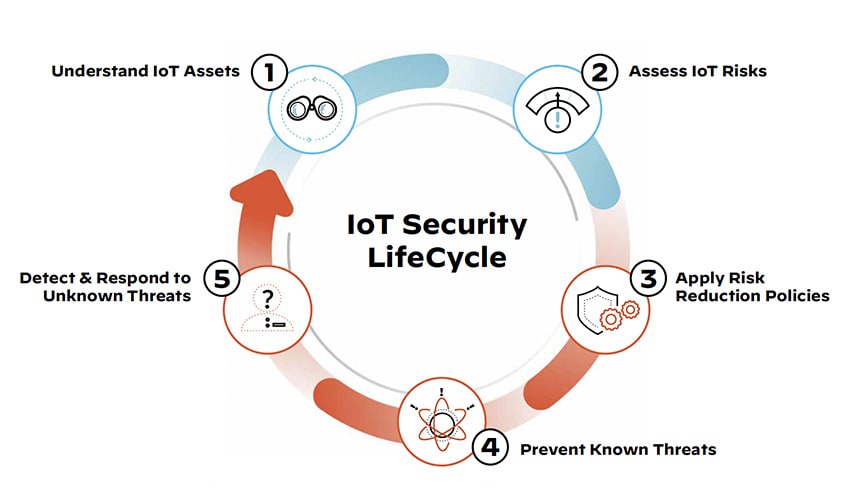
Network security and operations teams should be incorporating IoT security into standard practice, process and procedure to ensure both managed and unmanaged devices fall within the same level of visibility and control across the IoT security lifecycle:
Identify all managed and unmanaged devices with context.
Accurately assess and identify vulnerabilities and risks associated with all devices.
Automate Zero Trust policies and enforcement of those policies.
Take swift action on preventing known threats.
Rapidly detect and respond to unknown threats.
An effective strategy for security in IoT must protect devices and the networks they are connected to from the ever-widening spectrum of IoT security risks. To learn more about IoT security best practices, read The Enterprise Buyer’s Guide to IoT Security.
Reference
Unit 42® IoT Security Threat Report
Related Articles
How to Secure IoT Devices in the Enterprise
Zero Trust for Infrastructure: A Key Step in Addressing IoT Security Risks
Know Your Infusion Pump Vulnerabilities and Secure Your Healthcare Organization