VPN Security: Are VPNs Safe and Secure?
VPNs are generally safe for transmitting data over the internet but aren’t 100% secure. A VPN doesn’t constitute a complete cybersecurity strategy.
VPNs protect data in transit, preventing unauthorized access and data breaches. But VPNs can have vulnerabilities and don’t address all security risks. While they’re a critical part of enterprise security, VPNs should be integrated into a layered defense strategy.
What Makes a VPN Secure?
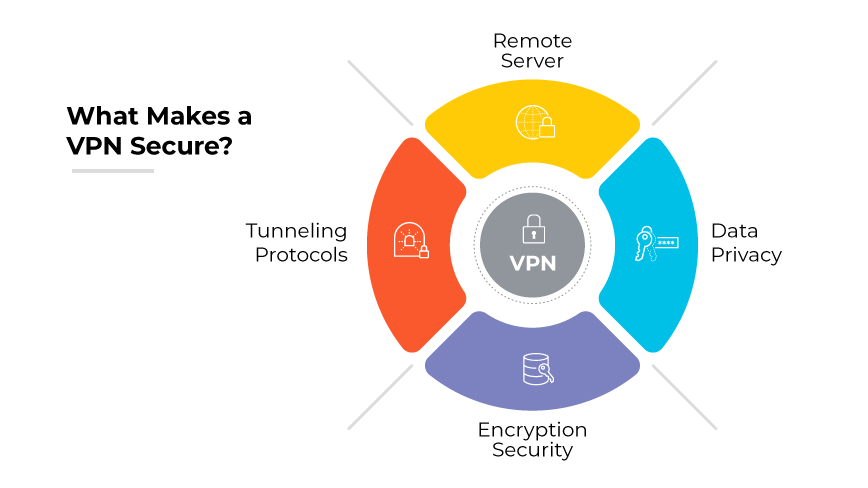
A virtual private network (VPN) serves as a secure channel for transmitting data over the internet. A VPN works by establishing an encrypted tunnel between a user's device and a remote server. It then masks the user's IP address, which enhances privacy and protects data from interception.
VPN security depends on encryption and tunneling protocols. Encryption transforms readable data into encoded information that can only be deciphered with a correct key. Advanced Encryption Standard (AES) is widely adopted for its strength and efficiency in protecting data.
VPNs employ various tunneling protocols, such as Layer 2 Tunneling Protocol (L2TP) and Internet Protocol Security (IPsec), which establish and maintain secure network connections. These protocols are fundamental in preventing data leaks and safeguarding information as it traverses shared or public networks.
Evaluating the Security of Corporate VPN Solutions
Corporate VPNs integrate robust security measures to ensure the confidentiality, integrity, and availability of data. This includes strong encryption, secure tunneling protocols, and advanced authentication methods. Such measures mitigate the risks of data interception and unauthorized access.
VPNs impact an enterprise’s security posture by extending its secure environment beyond physical offices. They create a controlled, encrypted network space that allows secure remote access and compliance with stringent data protection laws. VPNs also enable enterprises to monitor and manage network access, which is key for detecting and responding to security threats in a timely manner.
Understanding both the strengths and limitations of VPNs allows businesses to make informed decisions about network security strategies and choose solutions that balance performance with protection.
The Advantages of Using a VPN in Enterprises
The deployment of VPNs within businesses provides a shield against data breaches. By encrypting data in transit, VPNs prevent unauthorized entities from accessing sensitive information.
Secure remote access is another significant benefit, as VPNs allow employees to connect to the enterprise network from any location without compromising security.
VPNs are instrumental in ensuring businesses meet various compliance requirements by maintaining high data protection standards.
The Cons of Using a VPN in Enterprises
Despite their advantages, VPNs are not without potential drawbacks.
VPN protocols may have vulnerabilities that cyberattackers could exploit. VPN infrastructure management can be complex, requiring dedicated resources and expertise.
Additionally, VPNs can introduce latency and bandwidth challenges, particularly when the number of remote users is large. This can impact the speed and efficiency of network connections, leading to delays in data transmission.
Common Threats to VPN Security
VPNs can face various security threats that can compromise data integrity and confidentiality.
One prevalent threat is man-in-the-middle or meddler-in-the-middle (MitM) attacks, where an unauthorized actor intercepts communications between a user’s device and the VPN server. In such instances, attackers can potentially capture and manipulate data.
Additionally, malware over VPNs poses a significant risk. Even with encrypted connections, if a device is compromised, malware can traverse through the VPN tunnel, leading to possible infiltration of the enterprise network.
Best Practices for VPN Safety and Security
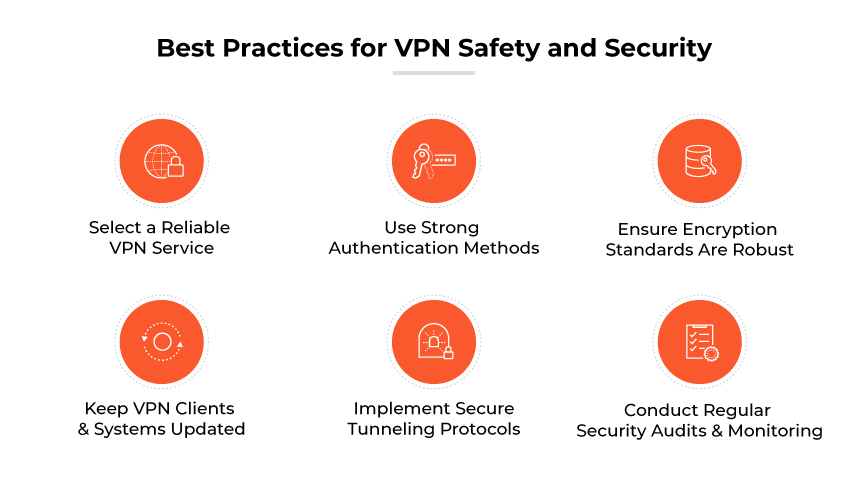
Select a Reliable VPN Service
When choosing a VPN, consider a service that provides VPN encrypted communication with a proven track record of reliability and customer support. A good VPN should offer a comprehensive level of security, featuring advanced encryption to protect data effectively.
Use Strong Authentication Methods
To enhance VPN security, implementing strong authentication methods is critical. This means moving beyond basic password protection and employing multifactor authentication (MFA). MFA requires users to present two or more pieces of evidence, or factors, to gain access. This adds a layer of security by ensuring that only authorized VPN users gain access.
These factors can include something you know (like a password), something you have (like a mobile device), or something you are (like a fingerprint). Multifactor authentication is recommended for verifying user identities before they can connect to a VPN.
Ensure Encryption Standards Are Robust
Encryption is the cornerstone of VPN security, obscuring data to prevent unauthorized reading. Enterprises should use the most current and robust encryption standards, like the Advanced Encryption Standard (AES) with 256-bit keys. This level of encryption is considered highly secure, making it a suitable choice for protecting sensitive enterprise data as it traverses the VPN tunnel.
Keep VPN Clients and Systems Updated
Regular updates to VPN clients and associated systems are vital for closing security gaps. Developers often release patches and updates to address vulnerabilities as they are discovered. By keeping VPN software up to date, enterprises can protect themselves against known exploits that cyberattackers might use to gain access to network traffic or bypass security measures.
Implement Secure Tunneling Protocols
Choosing secure tunneling protocols is essential for a safe VPN. Protocols like IPsec and OpenVPN provide strong security features that are necessary for protecting data in transit. It is important to select protocols that support high levels of encryption and can effectively prevent data leaks and exposure.
Conduct Regular Security Audits and Monitoring
Regular security audits and consistent monitoring help detect potential security incidents early. Audits can reveal vulnerabilities, ensure policy adherence, and validate that the VPN configuration meets security requirements. Continuous monitoring allows for the immediate detection of suspicious activities, enabling rapid response to threats.
Are VPNs Enough for Enterprise Security?
Virtual private networks (VPNs) are critical in today’s enterprise cybersecurity landscape. They create secure connections over public networks, ensuring that data remains encrypted and inaccessible to unauthorized parties. VPNs are crucial for safeguarding data in transit, particularly for remote workers accessing corporate resources from various locations.
However, the threat landscape is evolving, and reliance on VPNs alone is not sufficient. Cyberthreats have become more sophisticated, and attackers often target multiple layers of an organization's infrastructure. While VPNs protect data on the move, they do not inherently secure endpoints from malware or intercept advanced persistent threats within the network.
Beyond VPNs, additional measures such as secure web gateways (SWG), secure access service edge (SASE), and software-defined wide area networks (SD-WAN) have become integral to a comprehensive security posture.
SWGs, for instance, protect users from online threats by enforcing company policies and filtering unwanted software from user-initiated web traffic.
SD-WAN technology allows organizations to route traffic efficiently across wide area networks, while also providing enhanced security features. It simplifies the management and operation of a WAN by decoupling the networking hardware from its control mechanism. This improves performance and enhances security by allowing for centralized policy management. SD-WAN also integrates services directly into the network fabric.
SASE combines network security functions with WAN capabilities to support the dynamic, secure access needs of organizations. It converges network and security point solutions into a unified, global cloud-native service. SASE is tailored to address the security challenges of the modern enterprise. It provides secure network access from any location and on any device.
In scenarios where employees are accessing the network from various devices and locations, a VPN may serve as the first line of defense in online security. However, additional layers, like those provided by SASE, are required to manage access, protect user identities, control cloud usage, and secure web gateways.
As part of a broader cybersecurity strategy, it’s essential to position VPNs alongside these additional security measures. A comprehensive approach is key to protecting against the varied threats that enterprises face today. The goal is to create a security ecosystem that is adaptable, integrated, and complete. This ensures the privacy of data in transit and the overall security of the network and its resources.